Adaptive Spiking Neural Networks for Real-Time Multi-Object Detection Tasks [to appear]
Donghwa Kang, Woojin Shin, Cheol-Ho Hong, Brent Byunghoon Kang, Jinkyu Lee and Hyeongboo Baek
Design Automation Conference (DAC) 2026
Timestep-Compressed Attack on Spiking Neural Networks through Timestep-Level Backpropagation [to appear]
Donghwa Kang, Doohyun Kim, Sang-Ki Ko, Jinkyu Lee, Hyeongboo Baek, Brent ByungHoon Kang
Annual Association for the Advancement of Artificial Intelligence (AAAI) 2026
Software Supply Chain Security Guidance
Contributed by Minjoon Park, Changil Lim, Changjo Yun, Brent Byunghoon Kang
Ministry of Science and ICT, and National Intelligence Service, and Presidential Committee on the Digital Platform Government [PDF]
Towards scalable and configurable simulation for disaggregated architecture
Daegyeong Kim, Wonwoo Choi, Chang-il Lim, Eunjin Kim, Geonwoo Kim, Yongho Song, Junsu Lee, Youngkwang Han, Hojoon Lee, Brent Byunghoon Kang
Simulation Modelling Practice and Theory (SIMPAT) 2023 [PDF]
[BIBTEX]
[SOURCE]
OpenSGX: An Open Platform for SGX Research
Prerit Jain, Soham Desai, Seongmin Kim, Ming-Wei Shih,
JaeHyuk Lee, Changho Choi, Young Shin, Taesoo Kim, Brent Byunghoon Kang, Dongsu Han
23nd Annual Network and Distributed System Security Symposium, NDSS 2016 (15.4%) [PDF] [BIBTEX]
Efficient Kernel Integrity Monitor Design for Commodity Mobile Application Processors
Ingoo Heo, Daehee Jang, Hyunggon Moon, Hansu Cho, Seungwook Lee, Brent Byunghoon Kang, and Yunheung Paek
Journal of Semiconductor Technology and Science [PDF] [BIBTEX]
SeCReT: Secure Channel between Rich Execution Environment and Trusted Execution Environment
Jinsoo Jang, Sunjune Kong, Minsoo Kim, Daegyeong Kim and Brent Byunghoon Kang
22nd Annual Network and Distributed System Security Symposium, NDSS 2015 (Acceptance rate 16.6% (50/302)) [PDF] [BIBTEX] [PRESENTATION]
ATRA: Address Translation Redirection Attack against Hardware-based External Monitors
Daehee Jang, Hojoon Lee, Minsoo Kim, Daehyeok Kim, Daegyeong Kim and Brent Byunghoon Kang
Proceedings of the 2014 ACM SIGSAC Conference on Computer and Communications Security (CCS) (Acceptance rate 19.5% (114/585)) [PDF] [BIBTEX] [PRESENTATION]
Rosemary: A Robust, Secure, and High-performance Network Operating System
Seungwon Shin, Yongsoo Song, Taekyung Lee, Sangho Lee, Jaewoong Chung, Phillip Porras, Vinod Yegneswaran†, Jiseong Noh and Brent Byunghoon Kang
Proceedings of the 2014 ACM SIGSAC Conference on Computer and Communications Security (CCS) (Acceptance rate 19.5% (114/585)) [PDF] [BIBTEX]
KI-Mon: A Hardware-assisted Event-triggered Monitoring Platform for Mutable Kernel Object
Hojoon Lee, Hyungon Moon, Daehee Jang, Kihwan Kim, Jihoon Lee, Yunheung Paek and Brent Byunghoon Kang
13th USENIX Security Symposium (USENIX Security 2013) (Acceptance rate: 15.9% (44/277)) [PDF] [BIBTEX]
Vigilare: Toward Snoop-based Kernel Integrity Monitor.
Hyungon Moon, Hojoon Lee, Jihoon Lee, Kihwan Kim, Yunheung Paek and Brent Byunghoon Kang
Proceedings of the 2012 ACM SIGSAC Conference on Computer and Communications Security (CCS) (Acceptance rates: 17.2%, 14%, 18.9%) [PDF] [BIBTEX]
DoubleGuard: Detecting Intrusions In Multi-tier Web Applications.
M. Le, A. Stavrou, B. Kang
IEEE Transactions on Dependable and Secure Computing, July-Aug. 2012, Volume: 9, Issue: 4 Page(s): 512-525.
[PDF] [BIBTEX]
Identifying Users with Application-Specific Command Streams
A. El-Masri, P. Likarish, H. Wechsler, B. Kang
Twelfth Annual International Conference on Privacy, Security and Trust (PST 2014) July 2014, REGULAR paper. (Acceptance rate 47/161 = 29%) [PDF] [BIBTEX]
Developing and Refining Infected-Host Enumeration Methods for Advanced Botnets
C. Nunnery and B. Kang
2012.12.25, Telecommunications Review, Vol. 22 Issue 6.
Entropy-Based Measurement of IP Address Inflation in the Waledac Botnet.
R. Weaver, C. Nunnery, G. Singaraju, and B. Kang
CERT FloCon 2011
Towards Complete Node Enumeration in a Peer-to-Peer Botnet.
B. Kang, E. Chan-Tin, C. Lee, J. Tyra, H. Kang, C. Nunnery, Z. Wadler, G. Sinclair, N. Hopper, D. Dagon and Y. Kim
ACM Symposium on Information, Computer & Communication Security (ASIACCS 2009) [PDF] [BIBTEX]
Hash History Approach for Reconciling Mutual Inconsistency
B. Kang, R. Wilensky, J. Kubiatowicz, Proceedings of 23rd International Conference on Distributed Computing Systems (ICDCS), 2003 (Acceptance rates: 17.7%, 17.7%, 13.8%)
[PDF] [BIBTEX]
Network Support for Mobile Multimedia using a Self-adaptive Distributed Proxy
Z. Mao, H. So, B. Kang and R. Katz
Proceedings of 11th International Workshop on Network and Operating Systems Support for Digital Audio and Video (NOSSDAV), 2001 (Acceptance rates: 33.3%, 30.5%, 30%)
[PDF] [BIBTEX]
Toward a Model of Self-administering Data
B. Kang and R. Wilensky
Proceedings of the first ACM/IEEE-CS Joint Conference on Digital Libraries (JCDL), 2001 (Acceptance rates: 30%, 25%, 33%)
[PDF] [BIBTEX]
Dissertation: “S2D2: A Framework for Scalable and Secure Optimistic Replication.”
B. Kang
Ph.D. Dissertation, 2004. UC Berkeley TechReport, UCB/CSD-04-1351, Committee: Robert Wilensky, John Kubiatowicz, Eric Brewer, and John Chuang Qualification Exam Area: Operating Systems (with Security) [PDF]
Utility Patent: "SYSTEM AND METHOD FOR IMPLEMENTING A HIDDEN SERVER".
Filed by George Mason University, January 12, 2012.
Sole Inventor, Publication number: US 2012/0180127, Publication date: July 12, 2012
Entropy-Based Measurement of IP Address Inflation in the Waledac Botnet
R. Weaver, C. Nunnery, G. Singaraju, and B. Kang, CERT/CC (Computer Emergency Readiness Team) Proceedings of FloCon 2011. [PDF]
Tumbling Down the Rabbit Hole: Exploring the Idiosyncrasies of Botmaster Systems in a Multi-Tier Botnet Infrastructure.
C. Nunnery, G. Sinclair and B. Kang
USENIX LEET 2010 [PDF]
The Waledac Protocol: The How and Why.
G. Sinclair, C. Nunnery and B. Kang
IEEE Malware 2009 [PDF]
Tracking Email Reputation for Authenticated Sender Identities.
G. Singaraju, J. Moss and B. Kang
CEAS 2008 [PDF]
Concord: A Secure Mobile Data Authorization Framework for Regulatory Compliance.
G. Singaraju and B. Kang
LISA 2008 [PDF]
RepuScore: Collaborative Reputation Management Framework for Email Infrastructure.
G. Singaraju and B. Kang
LISA 2007 [PDF]
Peer-to-Peer Botnets: Overview and Case Study.
J. Grizzard, V. Sharma, C. Nunnery, B. Kang and D. Dagon.
(Cited by 340 times since its publication in Fall 2007)
USENIX HOTBOTS 2007 [PDF]
Privilege Messaging: An Authorization Framework over Email Infrastructure
B. Kang , G. Singaraju, and S. Jain
USENIX 20th Large Installation System Administration Conference (USENIX LISA), 2006 [PDF]
RegColl: Centralized Registry Framework for Infrastructure System Management
B. Kang, V. Sharma, and P. Thanki
USENIX 19th Large Installation System Administration Conference (USENIX LISA), 2005 [PDF]
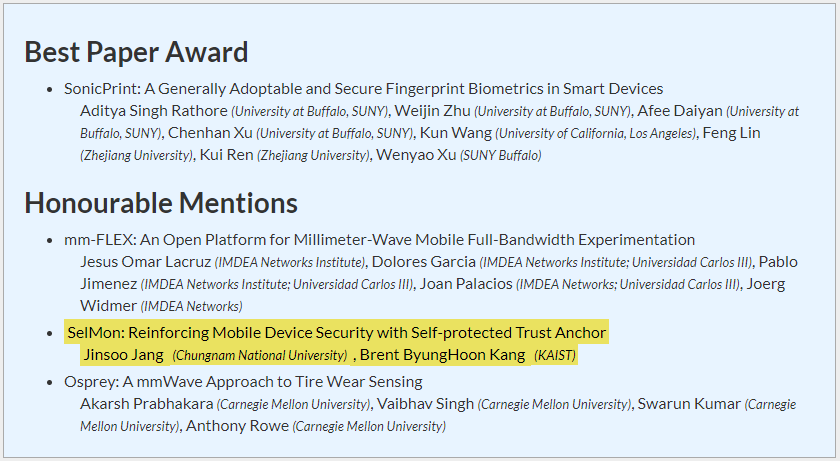 Prof. Jinsoo Jang and Prof. Brent Byunghoon Kang's collaborative team earned the "Best Paper Honourable Mention" from MobiSys 2020.
Prof. Jinsoo Jang and Prof. Brent Byunghoon Kang's collaborative team earned the "Best Paper Honourable Mention" from MobiSys 2020.  The CyberSecurity@KAIST International Workshop June 9(Sat), 2018, KAIST N1 building #102, Daejeon, Korea
The CyberSecurity@KAIST International Workshop June 9(Sat), 2018, KAIST N1 building #102, Daejeon, Korea The 19th World Conference on Information Security Applications August 23-25, 2018, Lotte City Hotel, Jeju Island, Korea
The 19th World Conference on Information Security Applications August 23-25, 2018, Lotte City Hotel, Jeju Island, Korea Daehee Jang won the prize money of 5 million won in his paper(RUMA: Rethinking Byte Granularity Heap Randomization) and took second place in the hacking defense contest which was held together.
Daehee Jang won the prize money of 5 million won in his paper(RUMA: Rethinking Byte Granularity Heap Randomization) and took second place in the hacking defense contest which was held together. 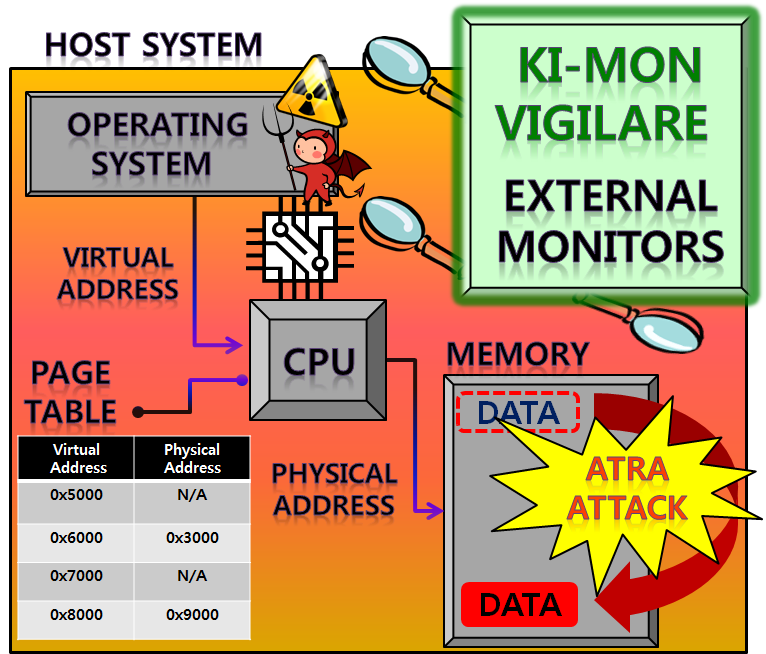 KI-MON and VIGILARE are new hardware-based security monitors designed to defend against OS rootkit attacks, however the recent discovery of “Address Translation Redirection Attack (ATRA)” calls for more robust monitor designs that can overcome the fundamental architectural limitation.
KI-MON and VIGILARE are new hardware-based security monitors designed to defend against OS rootkit attacks, however the recent discovery of “Address Translation Redirection Attack (ATRA)” calls for more robust monitor designs that can overcome the fundamental architectural limitation. pwnable.kr is a Wargame site which provides various challenges regarding educational system exploitation. CySecLab is running the pwnable.kr server which is created by one of our student.
pwnable.kr is a Wargame site which provides various challenges regarding educational system exploitation. CySecLab is running the pwnable.kr server which is created by one of our student. Four of the CySecLab members (PwnPineappleApplePwn) participated SECCON2016 International CTF competition and awarded 2nd place.
Four of the CySecLab members (PwnPineappleApplePwn) participated SECCON2016 International CTF competition and awarded 2nd place. Our team contributes to Islet, an ARM CCA-based confidential computing platform
Our team contributes to Islet, an ARM CCA-based confidential computing platform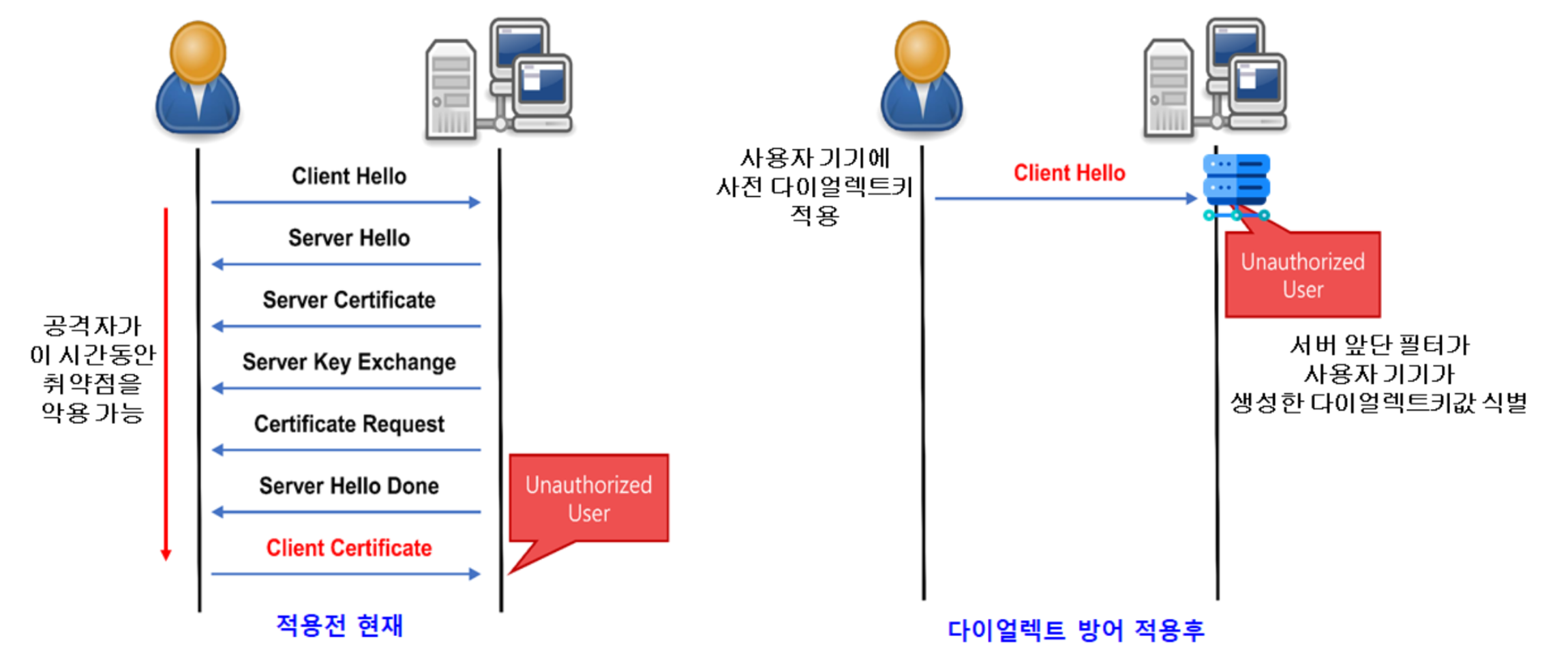 The protocol dialect technique is covered by the media
The protocol dialect technique is covered by the media
